CO2, water, and CH4 (methane) and some other minor gases are so-called “greenhouse gases” because they absorb infrared energy. However, be careful to avoid the common misunderstanding that the earth and its atmosphere behave like a garden greenhouse; that is not true. Greenhouses are closed systems except to incoming energy. Earth is an open system, open to receive energy, as well receive gases and other matter from space and also open to transmit energy, gases and matter back into space. A greenhouse is a poor analogy for earth’s climate.
Near earth’s surface, greenhouse gases re-emit almost instantly the energy they absorbed, emitting that energy at a slightly lower energy than which it was absorbed but emitting it into 3D space. Rarely is that emission mentioned in the news or by climate alarmists. Proponents of global warming want you to believe that energy is stored and builds up in the atmosphere in a sort of hothouse or pressure cooker, but that is not true.
In most locations, the concentration of water vapor (including clouds) in the atmosphere is far higher than CO2 and methane. That is, there are far more water vapor molecules in a given volume of air than there are CO2 or methane molecules. Near the equator and bodies of water, swamps and tundra, water vapor concentration in the air will be high. That is, the air is saturated, no more water vapor can be added to the air at that temperature and air pressure. Cold air holds very little water vapor. Cold air over cold water is also saturated, but air at the poles is usually very dry, water vapor concentration is very low. A volume of warm air holds much more water vapor than the same volume of cold air. Air in the tropics is usually humid.
The tropics and sub-tropics receive large amounts of solar radiation during the day, but none at night. During the day, the surface of ocean water is warmed by solar radiation and that warmth results in release of large amounts of CO2 and CH4 as well as water vapor into the atmosphere; the amount of these released gases dwarfs all emssions of these gases by humans. At night, the cooler ocean surface absorbs large amounts of CO2. CO2 is very soluble in cold water. A cold soda-pop keeps its bubbles.
The oceans and subsea floor hold far more methane (CH4) than all petroleum and fossil fuels ever discovered, and this methane is continuously degassed out of warm water and soil into the air. CH4 released into open air spontaneously converts (oxidizes) to CO2 and water at standard temperature and pressure. CH4 + 2 O2 -> CO2 + 2 H2O + a small amount of energy. Almost all CH4 originated as living cells. The cells died, entered the soil, rivers, lakes and ocean as runoff, metabolized and degraded by natural biological activity; this is the ultimate source of almost all fossil fuel on earth. That natural resource is continuously renewing and unlikely to be exhausted so long as there is life in the oceans.
Water vapor is the dominate greenhouse gas, absorbing by far both more direct solar energy and indirect solar energy re-emitted by the earth. More than 70% of the earth is covered with liquid water and about 40% of the earth and liquid water is receiving direct solar radiation every day. Additional liquid water is on land and in soil and plants. Solar radiation increases the molecular activity of liquid water molecules until they can no longer be held by the surface tension of the water. These active water molecules evaporate, i.e. release energetic water molecules, to become gaseous water vapor in the atmosphere. This release of energetic molecules cools the surface of the water, not warm the water, they just left. Your skin is cooled when your sweat evaporates.
Liquid water is far denser than air. Dense liquid water in the oceans is a huge reservoir of stored energy. The oceans contain greater than 1000 times more energy than the atmosphere; this means that earth’s atmosphere as a whole – regardless which gases make up the atmosphere – cannot warm the oceans in any significant amount. And this means the oceans are warming the atmosphere. The oceans are controlling the weather and climate on earth, not the atmosphere. The oceans are warmed by direct solar radiation as well as volcanic and tectonic forces resulting from gravity.
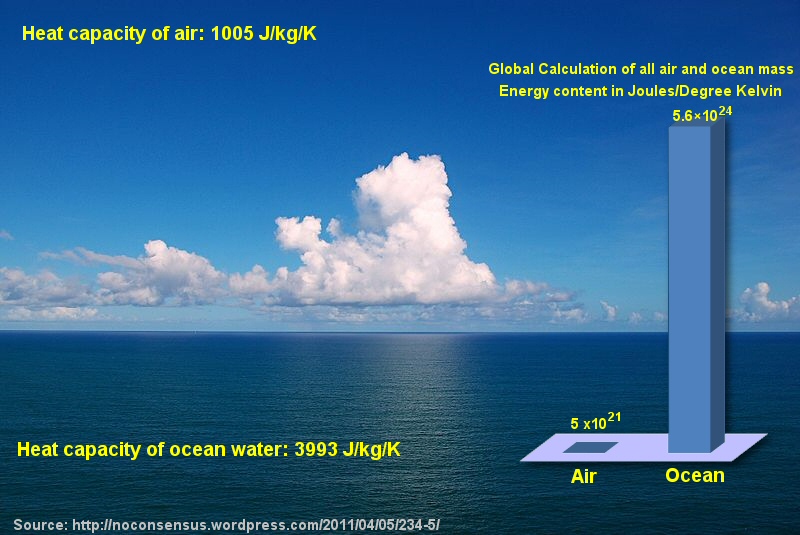
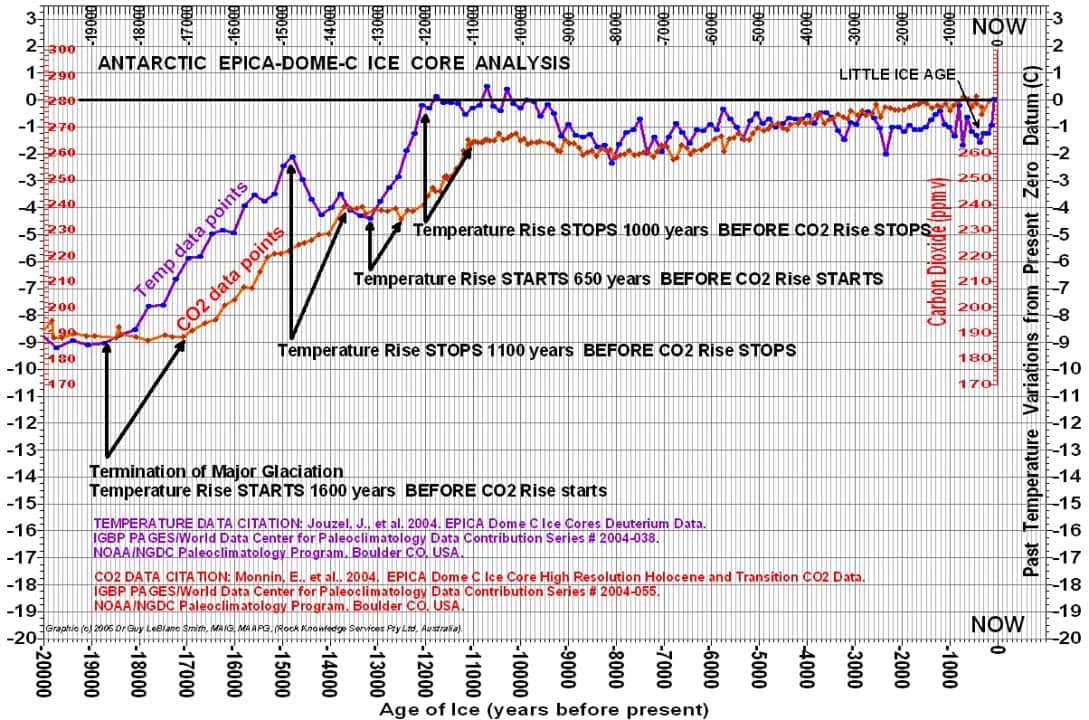
Figure 1
The specific gas molecules (nitrogen, oxygen, water vapor, as well as CO2, methane, and several other trace gases) that make up the atmosphere, each with their various concentrations, individually or in combination, are irrelevant to the long-term average temperature of the planet. In other words, an atmosphere of 100% CO2 could not significantly change the earth’s average temperature; instead, the ocean with its huge heat content would control the temperature of the 100% CO2 atmosphere. The atmosphere cannot warm significantly the earth over an extended time period, such as a year. But a warm ocean current, such as an El Nino, can change our climate and weather overnight.
However, water vapor and CO2 cause relatively minor temperature changes of the atmosphere at the surface (troposphere.) Water vapor and CO2 delay the release of energy from the earth into outer space, and this is most evident at night. Night time air temperatures at earth’s surface would be significantly cooler without water vapor and CO2. In a sense, greenhouse gases act as a nighttime insulator for the earth.
The effects of this are clearly seen at night. In warm, humid climates like New Orleans, the warmth of the air is retained late into the night, finally cooling by morning. Water vapor and CO2 do that. In dry desert or arctic areas, the warmth of the day very rapidly is re-radiated into outer space and nighttime temperatures plunge rapidly. The absence of water vapor and CO2 do that. CO2 has the same effect as water vapor/humidity except in far less amount than water vapor/humidity. CH4 is even less than CO2.
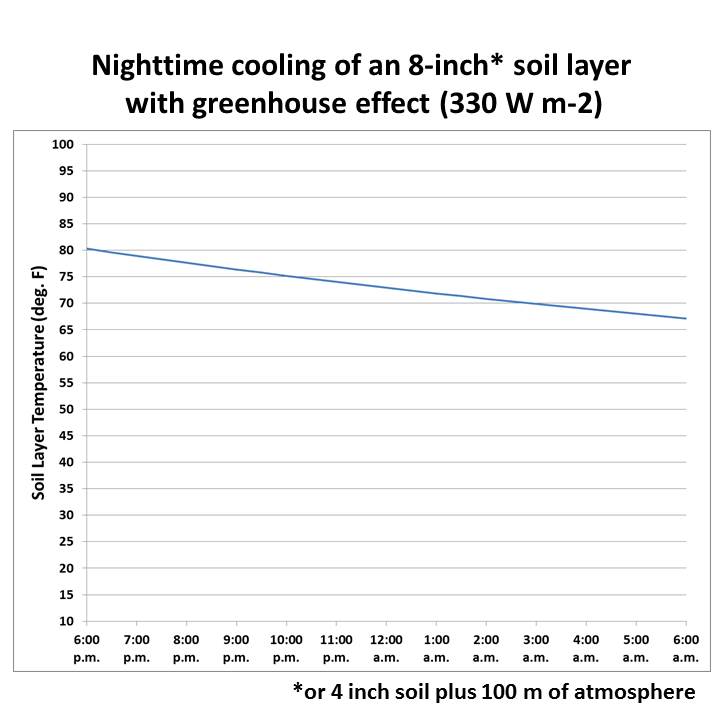
Figure 2
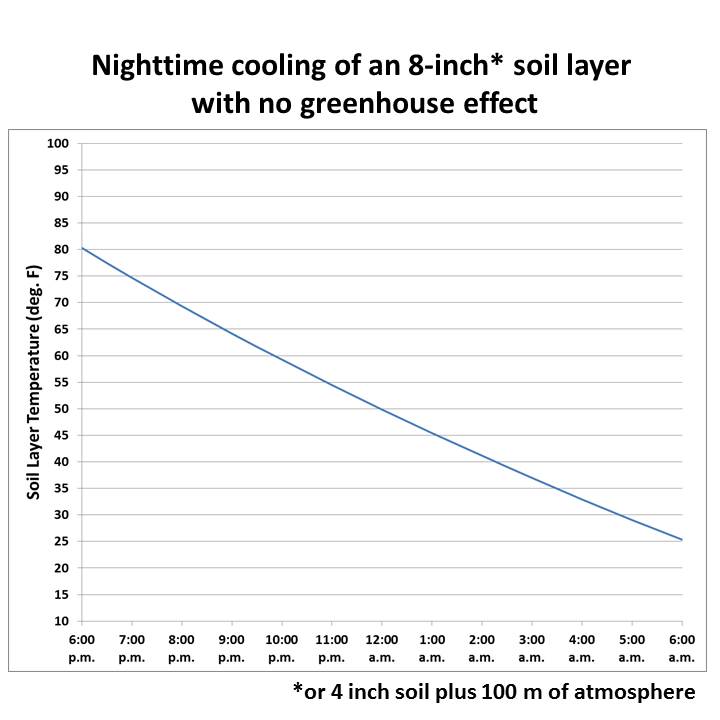
Figure 3
Nitrogen (78%), oxygen (21%) are the primary gases in the atmosphere, but these gases are mostly transparent to direct incoming solar radiation. Transparent means there are very limited or no energy bands available in these gaseous molecules to absorb energy at the wavelengths of the incoming solar radiation. A significantly large amount of solar energy is reflected by earth’s clouds, land and water surfaces back into outer space; this effect is known as albedo. The other atmospheric gases in total comprise about 1% of the atmosphere; this 1% includes water vapor, the inert gases (mostly argon which makes up 0.93%) and the trace gases. Carbon dioxide, methane and all other trace gases combined make up only about 0.04% of air.
Most radiant energy of the sun is transmitted through the gases in the atmosphere to the surface, i.e. to water and land surface, where it is absorbed. Most solar radiation is in the higher energy infrared, visible and ultraviolent wavelengths. Visible light, UV, X-Ray, and gamma radiation are all higher energy (higher frequency/shorter wavelength) than IR. Water vapor absorbs at certain visible energy bands…so we see darkening clouds as water vapor concentration increases. Solar radiation is absorbed by the molecules at the surface of water and land and then is spread through conduction and convection and dissipated in the energy cascade in the molecules of the water or solid matter. Some energy is re-emitted from the surface of land and water into the atmosphere but at lower energy, longer wavelengths, lower frequency than which it was originally absorbed.
Solar radiation received by the earth is known as Total Solar Irradiance (TSI). TSI has a cycle involving multiple variables which I will not go into here except to point out that climate cycles on earth correlate well with the TSI cycle and also with ocean temperature cycles known as PDO.
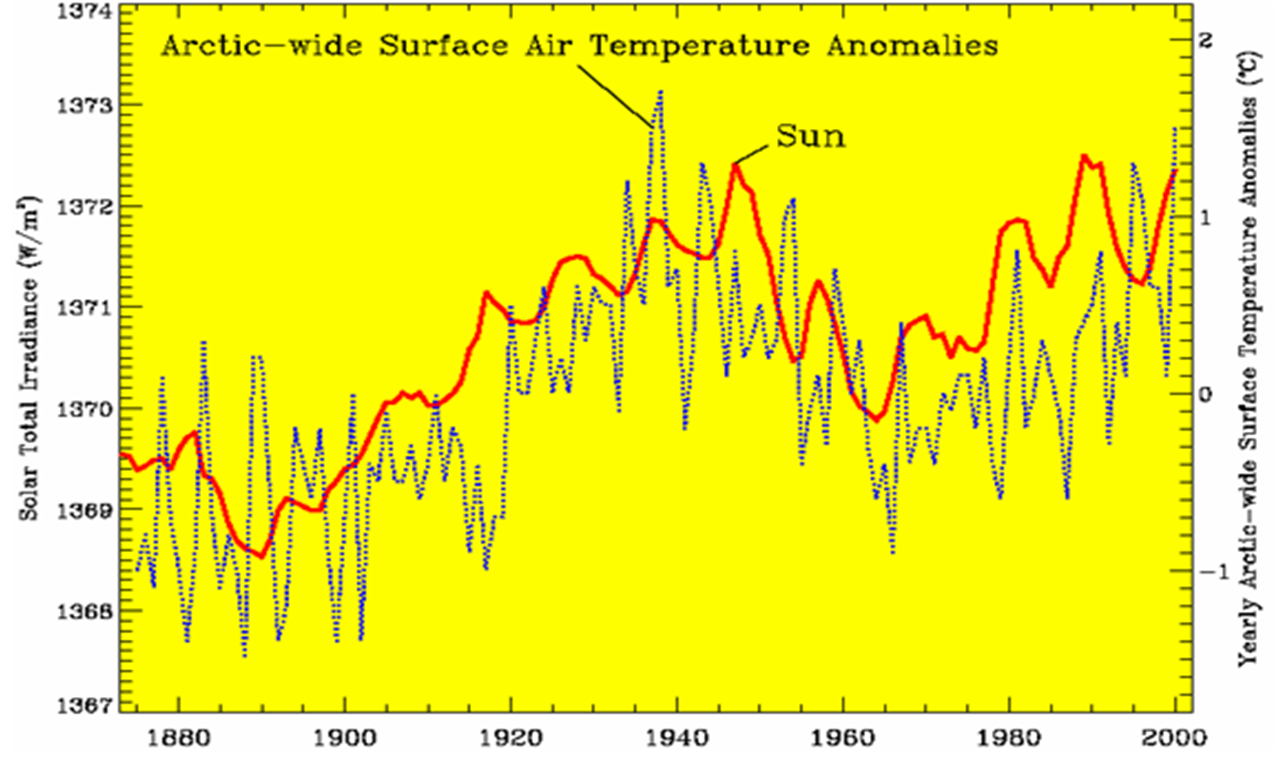
Figure 4
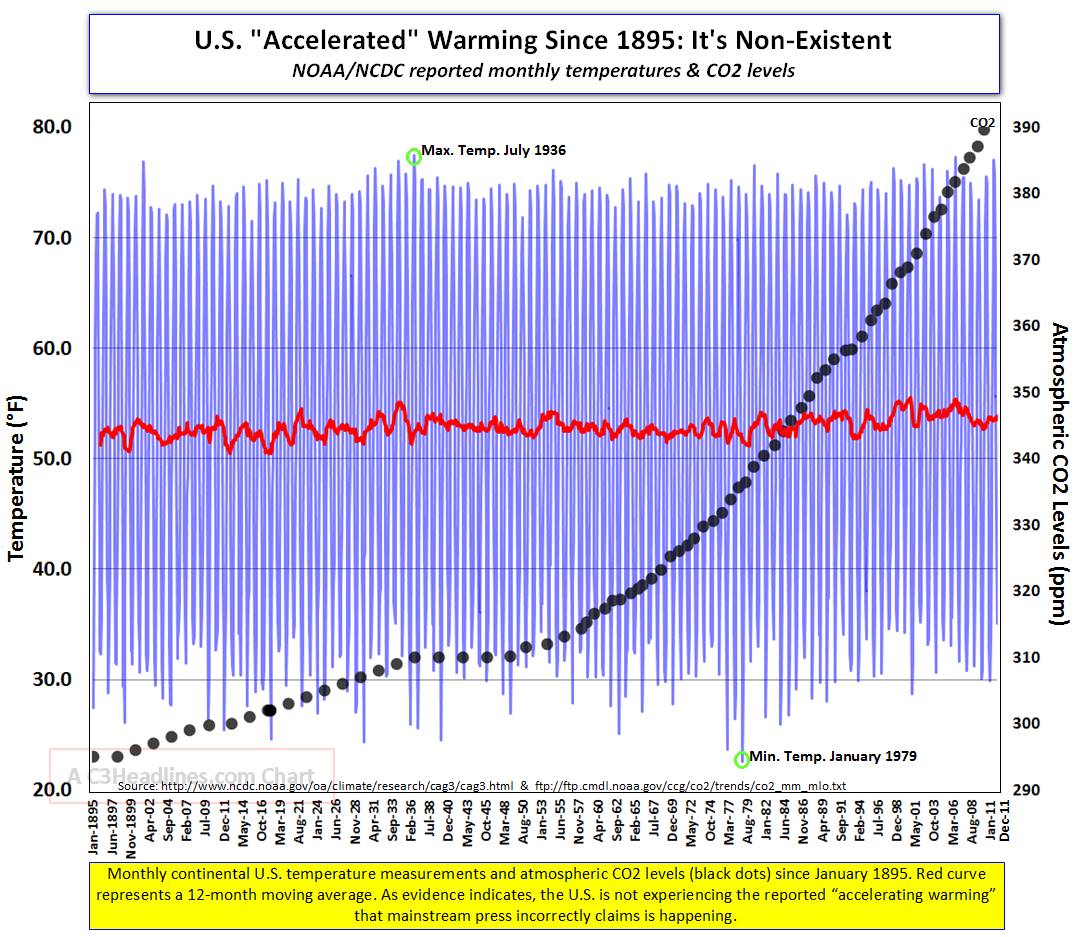
Temperature does not track CO2 very well (figure 11 below). Note temperature is flat, increasing, declining, and increasing while CO2 is increasing. Statistical correlation is weak.
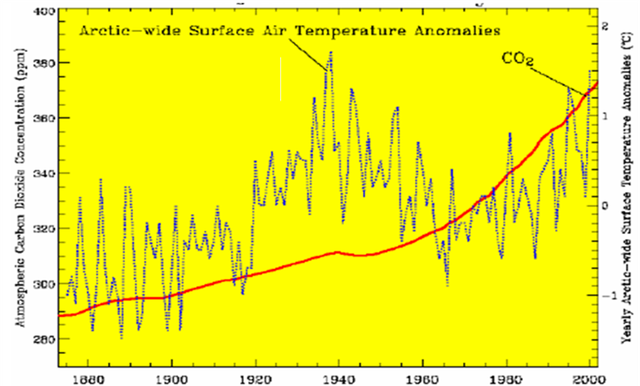
Figure 5
Over longer time periods, the correlation between CO2 and temperature is very poor. The two trends are widely diverging as seen in the graphic below. If the global warming hypothesis were valid, these two trends would be parallel or converging.
For the remainder of this discussion, I will consider only energy in the infrared (IR) wavelengths. Molecules in water and land absorb IR at several discrete higher energy/shorter IR wavelengths that match discrete energy bands of the electrons of each molecule. If the incoming energy does not match an energy band of the molecule, or if that energy band is not available to absorb because the band is already occupied with energy, then the energy passes through the molecule without being absorbed. If the IR energy is absorbed, then in a fraction of a second, part of that energy is dissipated as kinetic energy (various motions such as stretching, bending, and vibrations internal to the molecule or collisions with other molecules) leaving slightly lower energy/slightly longer wavelength/slightly lower frequency IR energy. That lower energy is then re-emitted. Since part of the energy has already been dissipated internally by the molecule, the emission has a longer wavelength, lower frequency of IR than the IR that was originally absorbed. Energy is not stored in a molecule except in the macro sense of all molecules taken together, and then only temporarily while the energy is progressively dissipated. Energy moves from one molecule to the next and at each step the energy is reduced. By this process, IR energy is absorbed by a water vapor, or CO2 molecule, or CH4 molecule for only fraction of a second and then re-emitted at a longer wavelength (lower frequency, lower energy, cooler). This cascade continues progressively downward in the energy until eventually the remaining energy is dissipated as kinetic energy by collision with other molecules, or various internal molecular motions.
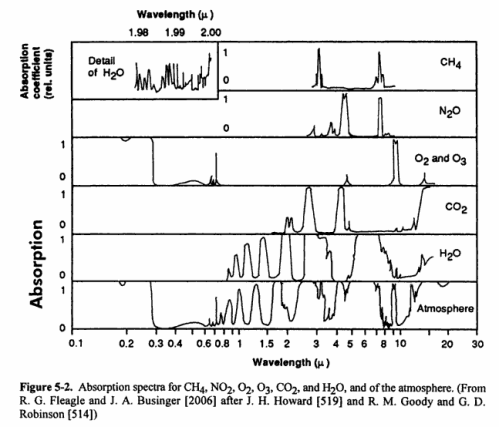
IR radiation is a sub-spectrum within the overall solar radiation spectrum. IR is 49.4% of solar energy reaching the outer atmosphere of earth. H2O, CO2, and CH4 absorb IR radiation ONLY at specific, discrete wavelengths (or quanta, or energy bands). Other wavelengths, which include most down-dwelling IR radiation directly from the sun, pass transparently through the molecules. Water vapor does absorb some incoming direct IR radiation. Some H2O, CO2, CH4 absorption wavelengths overlap (see graphic Figure 5-2), that is, these three molecules absorb IR at some of the same discrete wavelengths. This means that the gas which has the highest concentration in air absorbs and re-emits the most IR radiation. On average, water vapor including clouds is the highest concentration among the greenhouse gases, and thereby water vapor including clouds is the dominant greenhouse gas.
Most direct solar IR passes through air molecules to interact with molecules on the surface of water or land. Thus, infrared radiation is largely responsible for warming Earth’s surface, both land and water. In other words, the sun is not DIRECTLY warming the atmosphere, but INDIRECTLY warming the atmosphere. Most solar energy is absorbed in the molecules of the ocean and land which in turn warm the atmosphere. Most greenhouse warming is caused by reflected IR and IR emitted after dissipation from higher energy visible and UV energy. We don’t perceive visible light as heat; but when visible light interacts with matter, unless reflected, its energy is dissipated step by step in the downward energy cascade as described above until it becomes longer wavelength IR which then we perceive as heat. Re-radiation, conduction and convection from the surface of water and land warms the atmosphere.
IR energy only penetrates a few meters beneath the surface in liquid water in the oceans and lakes, while visible light transmits many meters beneath the surface of water, progressively loosing its colors from red to eventually higher energy blue and finally no visible light at increasing depth. The higher energy, shorter wavelength, higher frequency UV, x-ray and gamma energy mostly transmits through liquid water and finally interacts with molecules in solid matter in land or sea floor, or minimally with inorganic molecules dissolved in ocean water. Molecules on land and the seafloor surface are irradiated by these higher energy wavelengths, absorbing this energy, or conducting it further, and then these molecules progressively dissipate their energy as described above to progressively longer wavelengths and lower energy, eventually to IR wavelengths. The energy cascade continues on down the energy spectrum to satellite, wireless, radio, TV, MRI wavelengths and finally dissipated as kinetic motion of the molecule itself or collision.
The earth and the atmosphere also reflect and emit energy back into outer space, mostly in the visible and IR bands. IR emission from the atmosphere, water and land into outer space occurs day and night and is measured by satellite. Earth is an open system, continuously re-radiating its energy (which originally came from the sun) back into outer space, that is, radiating from higher energy earth to the much lower energy outer space beyond our atmosphere.
The fact that earth’s temperature is relatively stable over long periods of time, millions of years in multiple geological periods, implies that there is a balance between incoming energy and outgoing energy. I won’t go further into this energy balance topic here.
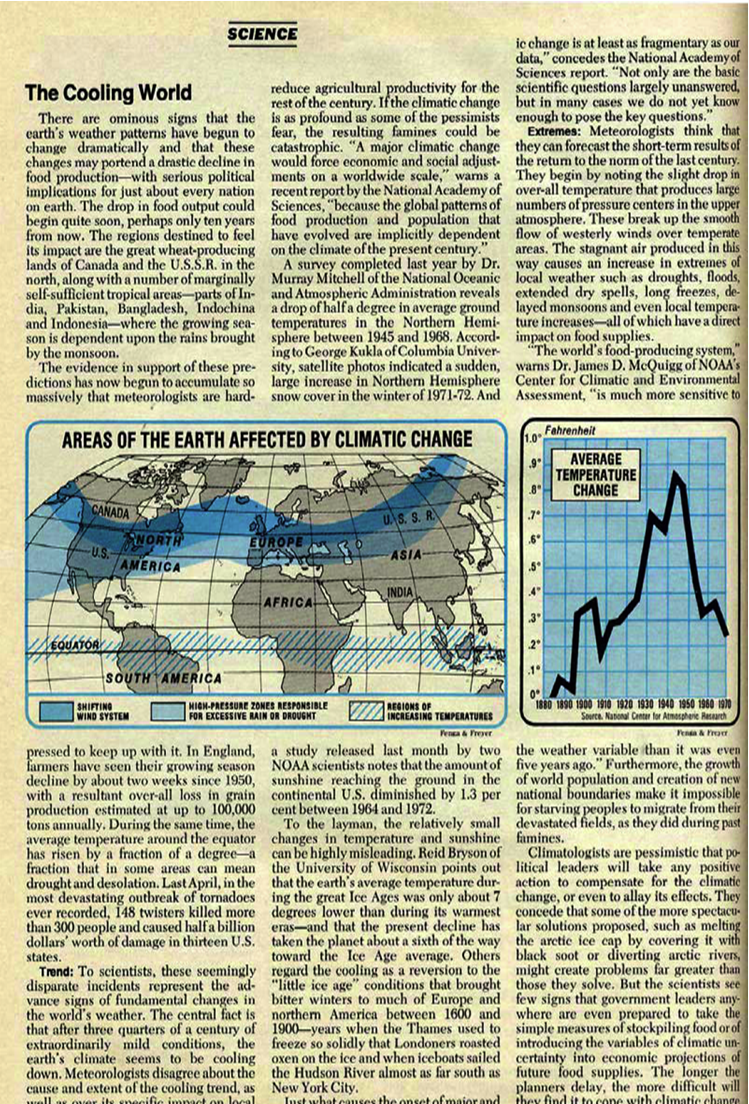
Over the very long time period of millions of years leading to the present, the earth has been in a slow cooling trend and has had a slowly declining atmospheric CO2 concentration as indicated in these graphics; this is probably contrary to what you have been told and taught.
On the other hand, and probably what you have been taught, in the geological short term, that is since the Little Ice Age and Industrial Revolution, earth warmed and total CO2 concentration increased. However most of that warming occurred before the 1950’s and that period was prior to the highest CO2 emissions by humans due to use of fossil fuels. In other words, the warming that followed the end of the Little Ice Age had very low CO2 concentration, thus that CO2 could not have caused the warming that occurred. The warming that occurred since the end of the Little Ice Age is within the statistical variation of the much longer-term cooling trend. In geological terms, since there is year-round ice at both poles, our present period is part of an interglacial period within an ice age.
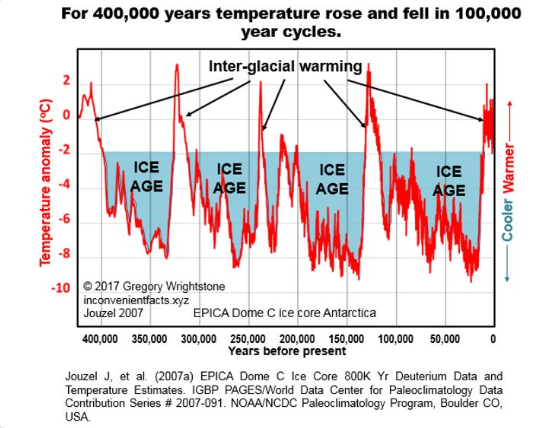
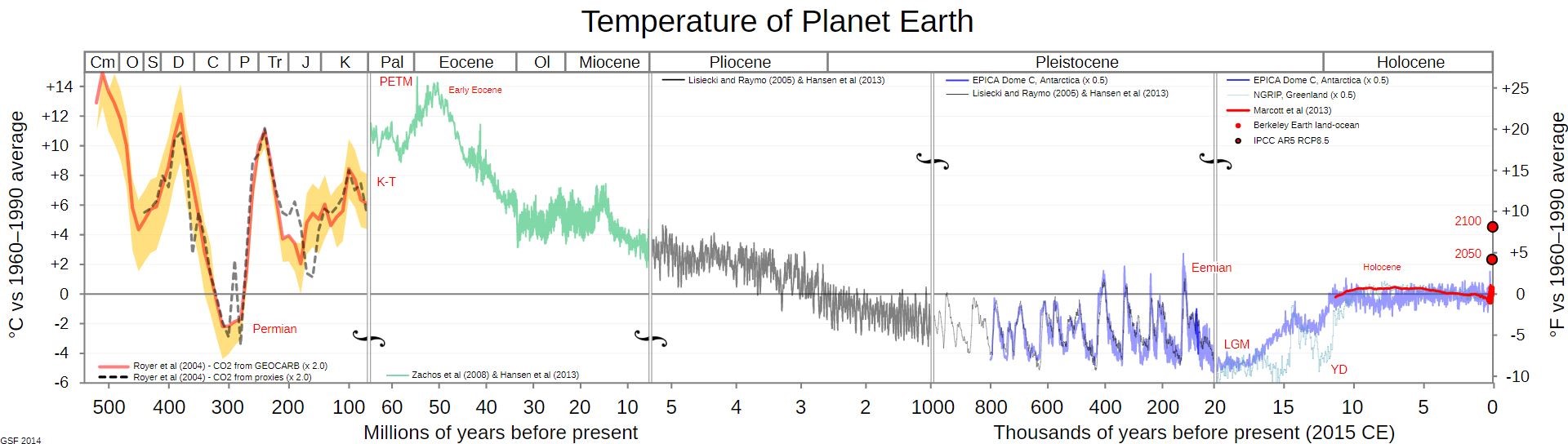
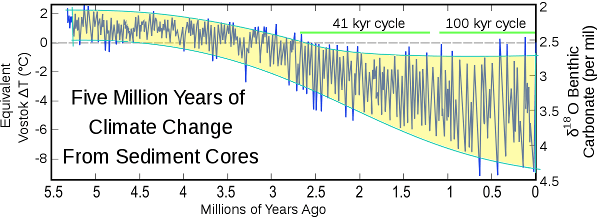
Figure 6
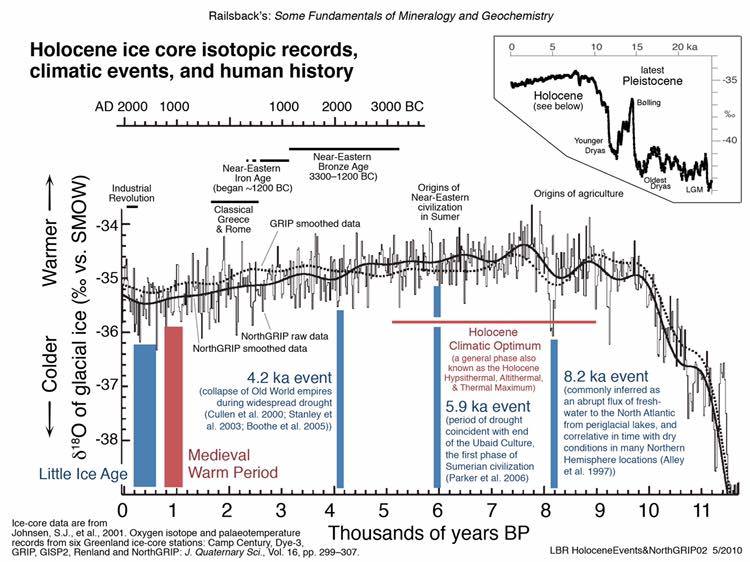
There has been global warming during our lifetime, mostly occurring before the 1950’s, but this warming is not unprecedented. And there has also been global cooling during our lifetime, also not unprecedented.
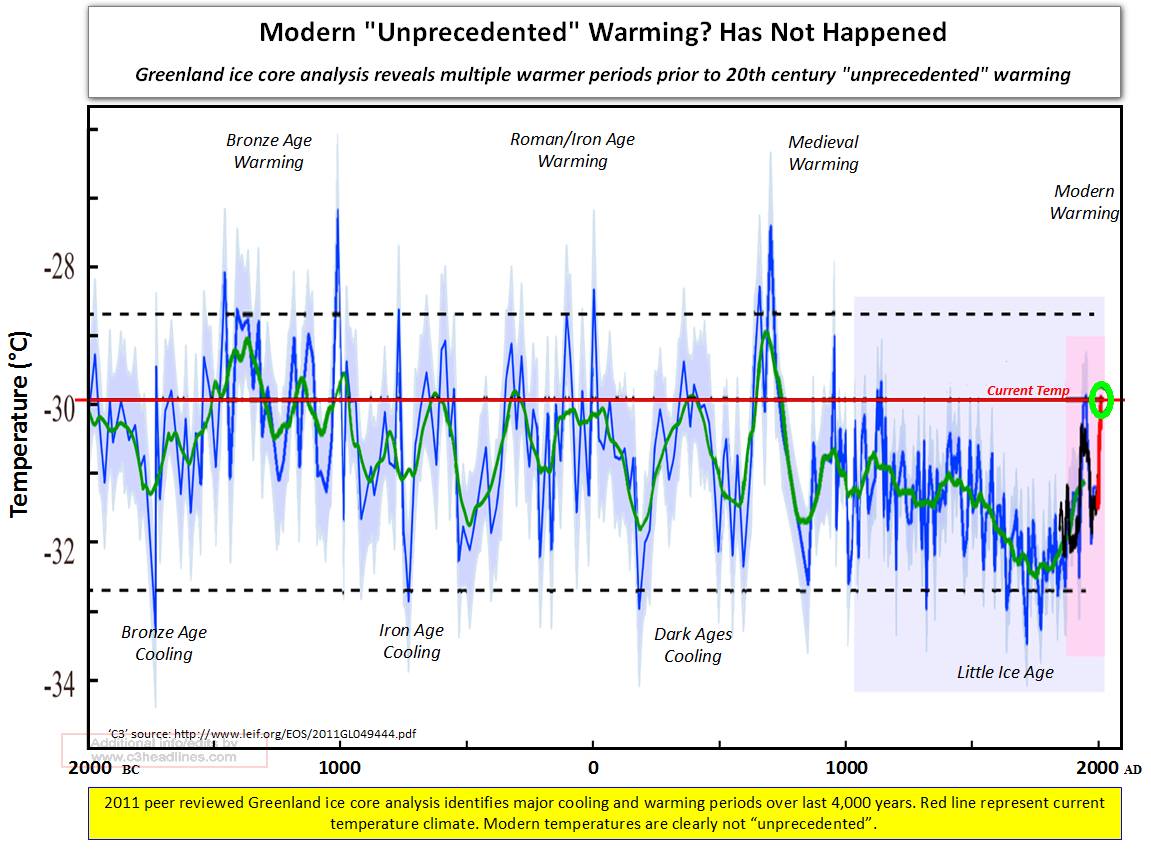
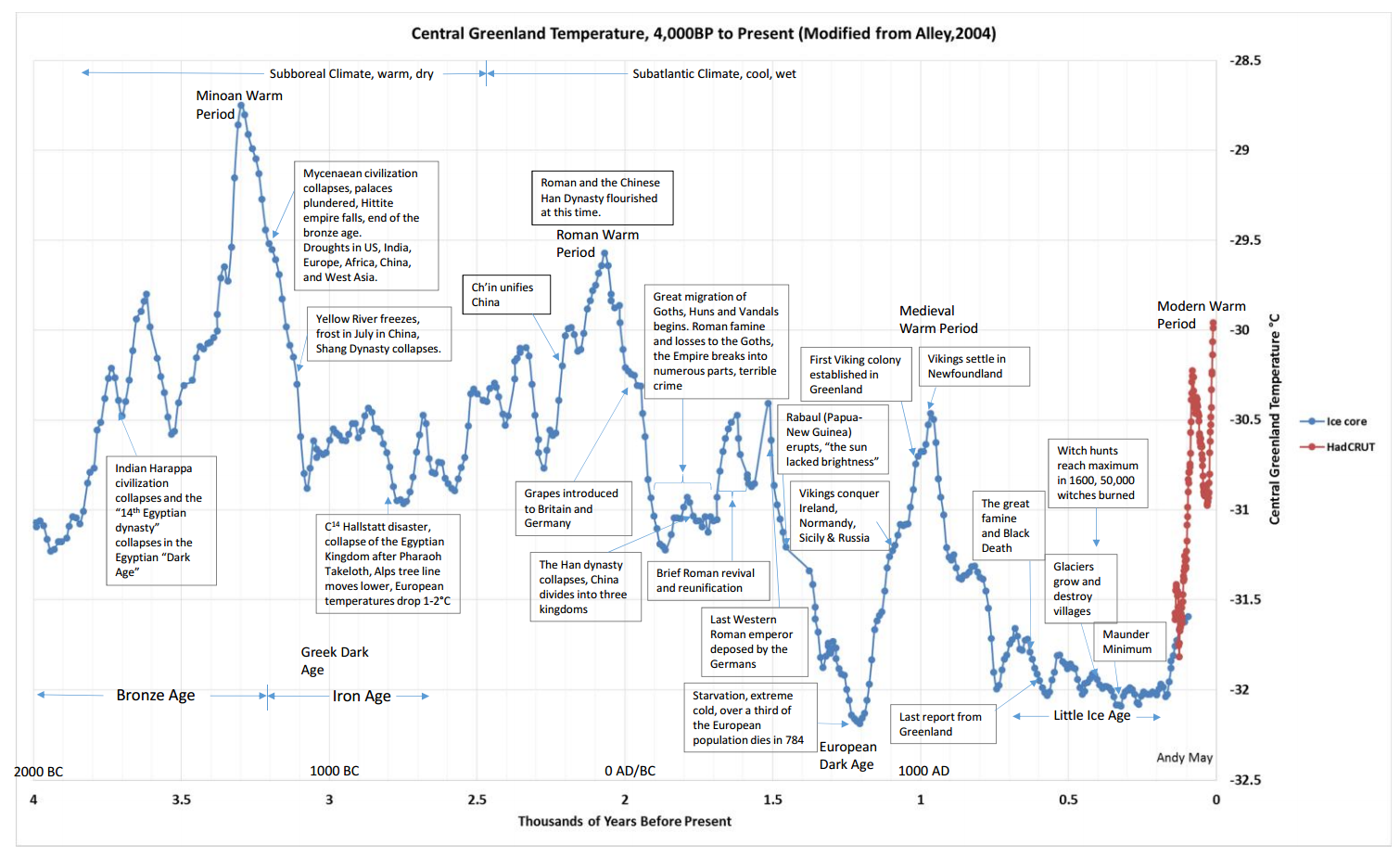
Figure 7
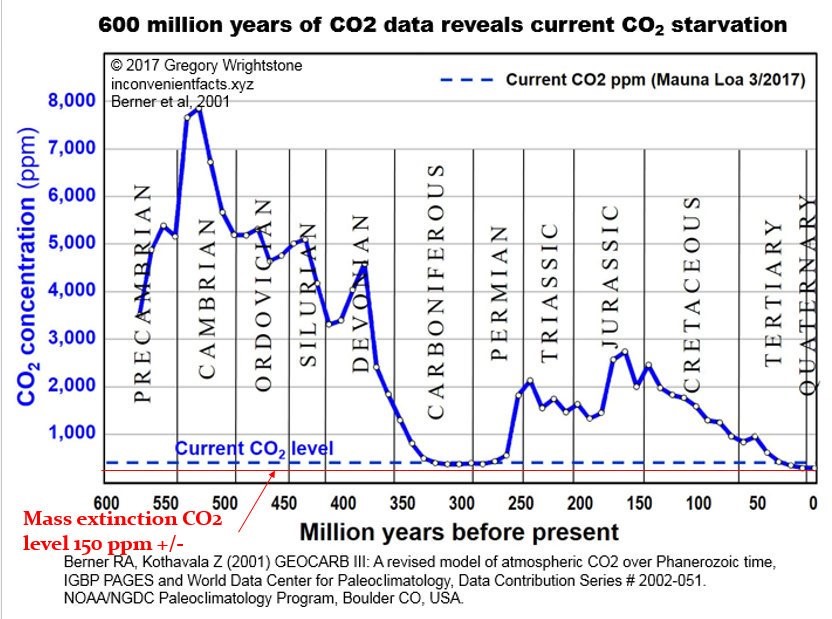
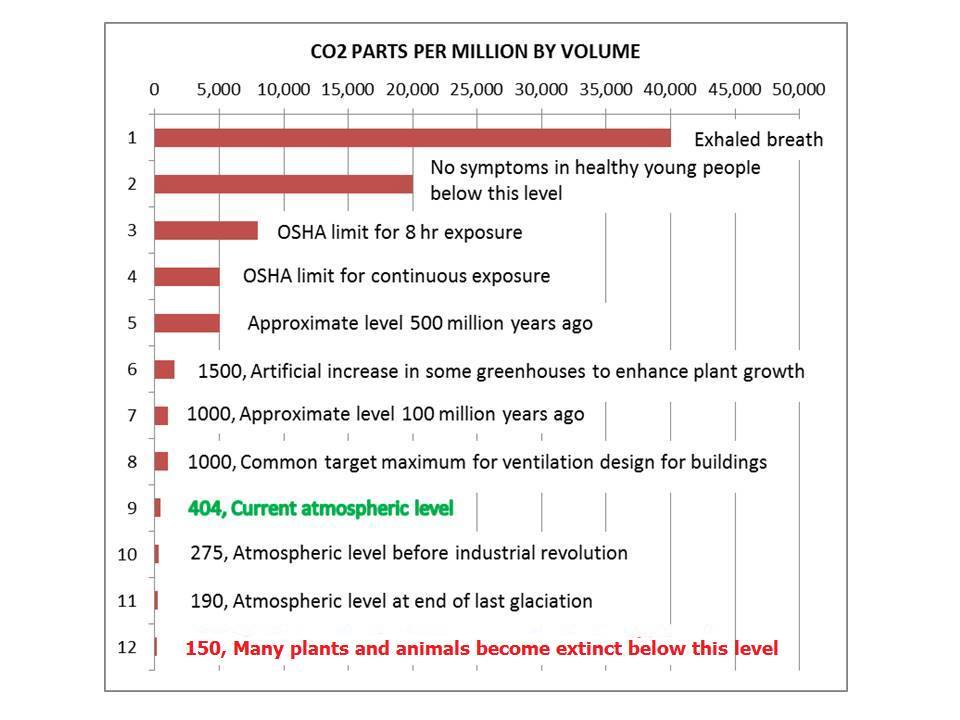
Figure 8
Returning to our “greenhouse gases,” the takeaway point is, again, the sun heats the earth, then the earth heats the atmosphere. The atmosphere is not heating the earth. According to the laws of thermodynamics, energy only flows from higher energy earth to the lower energy atmosphere. Earth (oceans and land) heat the air, not the reverse. Where can we measure this effect in the natural world? Detrended (i.e. seasons removed) sea surface temperatures versus air temperatures, we see in the graph below that increasing air temperature ALWAYS FOLLOWS increasing sea surface temperature. No matter how high the CO2 or methane concentrations are in the air, the ocean temperature will control the air temperature of the earth. In bulk, like insulation, water vapor, CO2, and methane temporarily delay but do not halt the continuous dissipation of energy/heat via the process described in the above paragraphs.
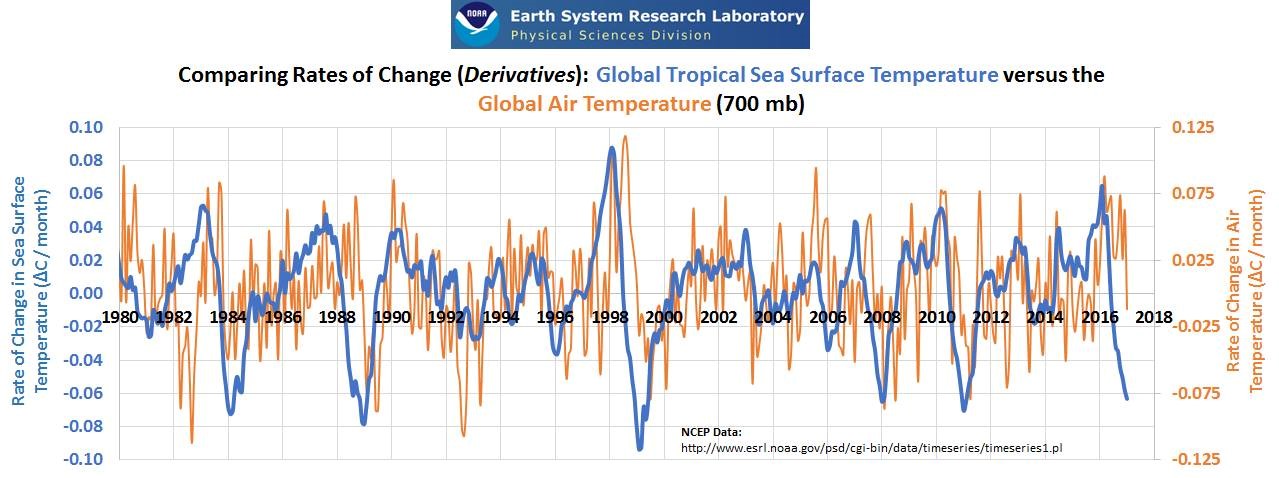
According to the proposed hypothesis for human-caused global warming (AGW), the continuing accumulation of CO2 in the atmosphere causes or forces increased warming in the atmosphere. The hypothesis requires disregarding the important facts that warming has currently stopped and also that there has been cooling for some periods in our lifetimes and historically, when according to AGW there should have been an increasing rate of warming due to the increasing concentration of CO2. Also, again falsifying the AGW hypothesis, when warming periods have occurred, there is no difference in the rate of warming during those periods despite the fact that CO2 has increased.
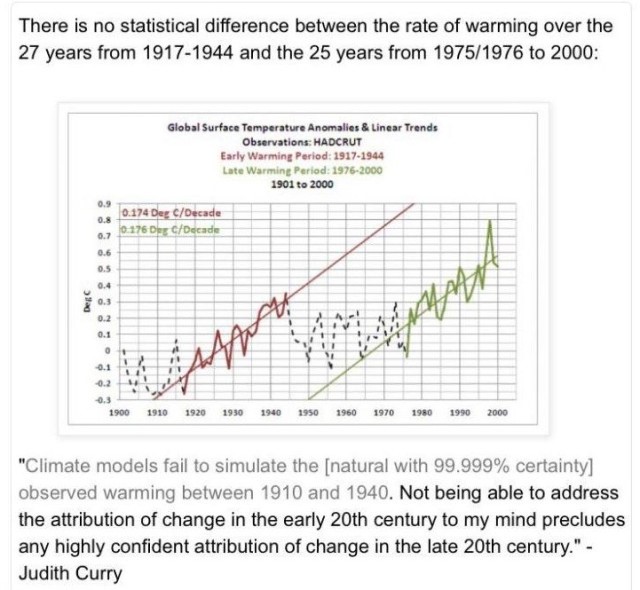
Figure 9
Based on a single molecule, one CH4 molecule absorbs more energy and re-emits more energy than one CO2 molecule, and one CO2 molecule absorbs more energy and re-emits more energy than one H2O molecule. But, the concentration (or abundance) of water vapor in air is about 1%, while the concentration of CO2 in air is only about 0.04% (or 400 ppm) and the concentration CH4 in air is only about 0.0018% (or 1.8 ppm). Thus more water vapor molecules in the air absorb more IR energy upgoing from the earth. Also, the IR radiation absorption wavelengths of water vapor overlap most of the IR radiation absorption wavelengths of CO2 and CH4. Since the concentration of water vapor is more than 10 times higher than that of CO2 and 100 times higher than CH4, the IR radiation emitted by the ocean, land and sun is more than 10 times more likely to be absorbed by water vapor molecules than by CO2 molecules and 100 times more likely to be absorbed by water vapor molecules than CH4 molecules. Then, when the water vapor, CO2 and CH4 molecules re-emit their energy upgoing and horizontally, or else collide, once again these emissions or collisions are far more likely to be interactions with a water vapor molecule; these phenomena change with increasing altitude.
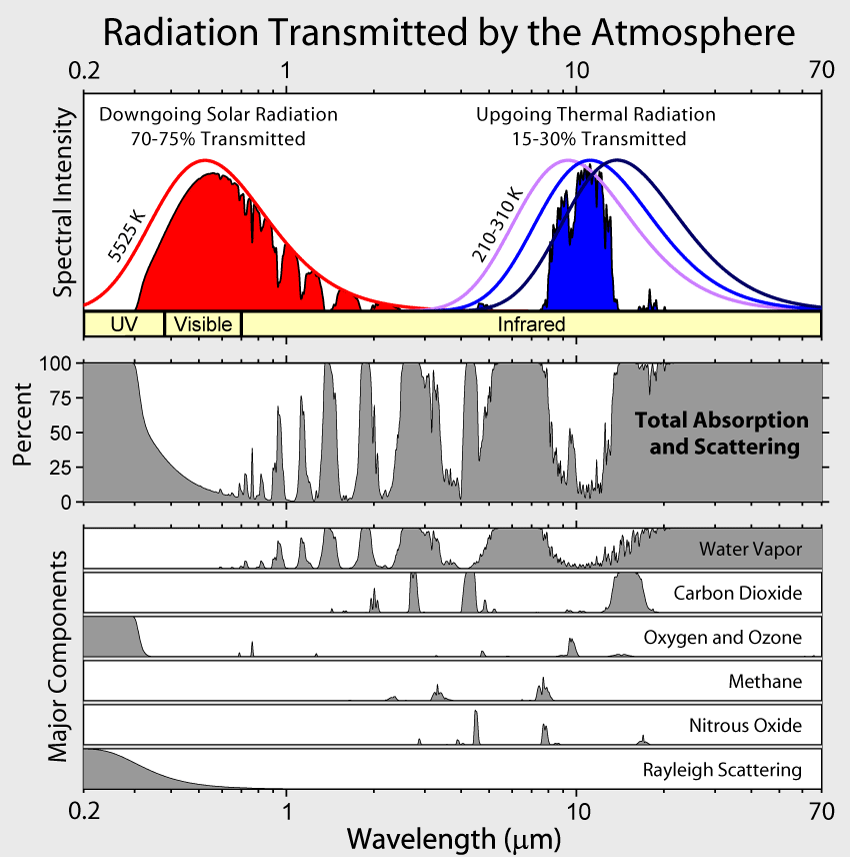
Figure 10
With regard to CO2 and CH4, the net result is that exponentially less warming results from each incremental increase in CO2 or CH4 concentration. The natural logarithm function is the inverse of the exponential function. The graphic below illustrates the natural log curve of temperature versus CO2 concentration that results from progressively increasing the CO2 concentration. In climatology terms, climate and temperature sensitivity are progressively diminished as CO2 concentration increases. Each doubling of CO2 concentration results in incrementally less warming, following a logarithmic progression. The available quantum energy bands of CO2 and CH4 are already occupied with energy received from nearby molecules. Adding more absorbing molecules decreases the mean-free-path of the radiation between molecules. Progressively higher levels of CO2 (and methane) produce progressively less warming. The absorbance of radiation is logarithmic.
Figure 11
Furthermore, of the approximate 400 ppm (or 0.04%) total CO2 concentration in earth’s atmosphere, humans from all sources emit only about 3% of that total. About 97% of atmospheric CO2 is natural. About 98.5% of total CO2 is absorbed by nature.
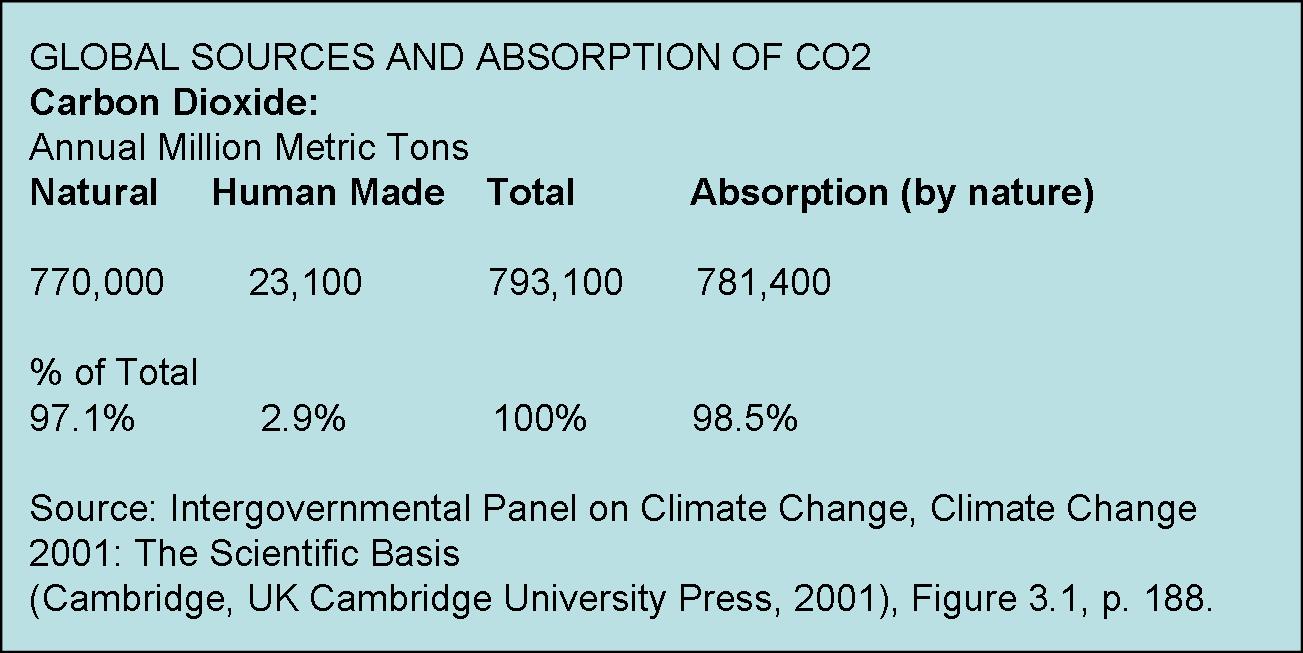
CO2 concentration has been increasing since the end of the Little Ice Age, around the time of the Industrial Revolution, primarily because earth has been slowly warming since that time. The human contribution is minimal. But, since CO2 is not causing significant warming (or even reproducibly measurable warming), and since the earth is in fact becoming greener according to NASA satellite studies, then there is no good reason to reduce CO2, or to reduce use of fossil fuels. Also, since most CO2 is natural, there is no practical way for humans to significantly reduce atmospheric CO2 concentration. Carbon sequestration, carbon offsets, carbon taxes, carbon trading are environmentally useless, harmful, economically wasteful, fraud. On the contrary, there are benefits to higher CO2, such as increasing crop yields. And there are also benefits to warming.
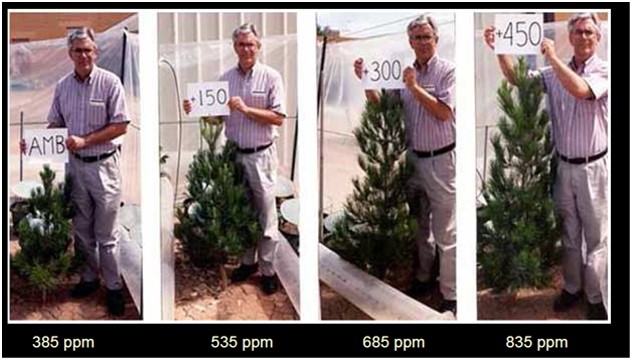
Figure 12
Despite clear evidence that the atmosphere is not significantly warming the planet, and under the laws of physics the atmosphere could not significantly warm the planet, still some politicians and scientists try to alarm citizens to persuade them that increasing CO2 and CH4 concentration forces catastrophically dangerous, large increases in temperature trends by increasing absorption of IR by water vapor. The alarmists’ torturous and unvalidatable hypothesis and models treat water vapor as part of a feedback system rather than as the dominant greenhouse gas. But, if this hypothesis were true, and it is not, since CO2 has been increasing steadily since the end of the Little Ice Age (CO2 increased about 150% from a very low CO2 level), then we should be seeing rapidly rising global temperature due to this feedback forcing effect, and we should be seeing a difference in rate of warming over time (or significant difference in second derivative.) However, the temperature trend has been only slightly increasing, and then only sometimes, and the warming trends are not exceptional or unprecedented in nature, and the overall temperature trend is diverging from the steadily rising CO2 trend.
If CO2 were the cause of warming, then the CO2 and temperature trends would be parallel or converging during the same time periods, and the CO2 increasing trend would occur before the warming trend; however, these correlations are not found in real world evidence unless the time periods are cherry-picked or the data has been manipulated. Even worse for the climate alarmists, there are multiple time periods, decades, where the temperature trend decreased while CO2 trend increased…for example the 1960s to late 1970s when most scientists and news outlets were proclaiming global cooling. CO2 cannot force both warming and cooling.
Climate catastrophe and gloom are entirely based on computer models, models which have never been validated against scientific observations.
Cover of Time magazine, January 31, 1977.
As of December 2018, the global temperature measured by satellites (the most accurate and reproducible measurement available), is only 0.45 degrees F above the average temperature computed since 1978 when satellite measurement began, meanwhile CO2 has been steadily rising during this same period. That’s not much warming; but the CO2 concentration is growing. In other words, nature has falsified the global warming hypothesis and climate models. Temperature has not been increasing in unison in correlation with increasing CO2. https://www.nsstc.uah.edu/climate/2018/december2018/GTR_201812Dec_1.pdf
Importantly, as shown in the graphic below, trends of increasing temperature precede trends of increasing CO2. Many peer-reviewed scientific papers confirm this observation. If CO2 were the cause or were forcing temperature increases, then that CO2 increase must precede the trend of increasing temperature; unfortunately for the AGW hypothesis and climate alarmists that evidence is not observed. Obviously, an effect cannot precede its cause. In other words, earth’s temperature is controlling CO2 concentration, not the other way around. (Al Gore’s science fiction movies show CO2 increases preceding or coincident with temperature increases leading up to a runaway ‘hockeystick’ warming.)
Most CO2 is emitted by the oceans and lands, naturally, by degassing caused by the slow warming trend since the Little Ice Age. Warmer water holds less CO2 than cold water. The relative partition ratio of a gas such as CO2 between water and air is controlled by Henry’s Law. Compared to the atmosphere, the oceans contain enormous energy (as already shown). Oceans contain about 50 times more CO2 than the atmosphere and 20 times more CO2 than the biosphere on land.
It would take 10,000 years for humans to change the temperature of the ocean by a mere 1 degree even if humans devoted all energy resources full time to that effort. The effects of the oceans on the earth’s climate are enormous, but the warming effect of human CO2 is trivially tiny.
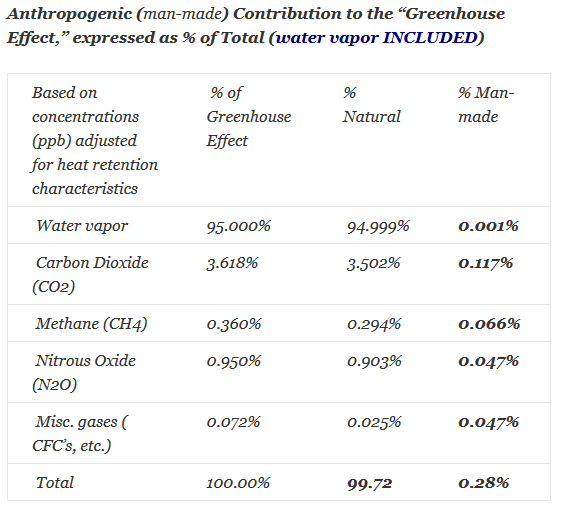
Figure 13
The claim that the relatively tiny amount of CO2 contributed to the atmosphere by humans is controlling earth’s temperature is falsified according to the rules of science. We mere humans are not able to change the temperature of earth by adding or subtracting CO2, no matter the amount of CO2. Even if the air were 40% CO2, an amount that is 1000 times higher than today’s total CO2 and 10,000 times higher than the human contributed CO2, the atmosphere can not significantly warm the oceans. Oceans are a gigantic heat sink or reserve, moderating the earth’s temperature and controlling earth’s climate.
This is NOT to say that humans do not affect temperature and climate in other ways, such as building cities, roads, planting or cutting forests and fields, etc. This IS to say that AGW, the hypothesis of human-caused global warming by the contribution of a mere 0.004% of the total CO2 emissions, is scientifically wrong. The human contribution to global warming is statistically insignificant, so tiny it is unmeasurable in the real world; the hypothesis of human-caused global warming/climate change has been falsified by real world observations and experiments.
What is really going on?
António Guterres, the current Secretary General of the UN, is the former president of Socialist International, which “was formed in London on 28 September 1864 by socialist, communist and anarchist political groups and trade unions. Tensions between moderates and revolutionaries led to its dissolution in 1876 in Philadelphia. The Second International was formed in Paris on 14 July 1889 as an association of the socialist parties.” (Wikipedia) With member organizations in more that 100 nations, following the communist tradition of Karl Marx, Leon Trotsky and Vladimir Lenin, Socialist International views the chief source of oppression and exploitation in the world to be capitalism — private property — whose inevitable by-products are poverty, environmental degradation, war, famine, and most other ills that plague humanity. UN leaders have also announced the UN’s anti-capitalist intentions. http://www.socialistinternational.org/viewArticle.cfm?ArticleID=1902
Bottom line: the global warming / climate change agenda is a giant, global fraud. The where, why, who, and when proponents knew it was a fraud is a subject for another day and a court of law. The global warming/climate change agenda is a global, political scheme to re-distribute wealth, change national economic systems away from capitalism, reduce national and individual sovereignty and reduce citizen control of private property, and hand over funding and control to unelected supra-national alliances and organizations like the UN and the EU.
References:
- https://www.omicsonline.org/open-access/New-Insights-on-the-Physical-Nature-of-the-Atmospheric-Greenhouse-Effect-Deduced-from-an-Empirical-Planetary-Temperature-Model.pdf
- Figure 2 and 3. http://www.drroyspencer.com/2015/04/why-summer-nighttime-temperatures-dont-fall-below-freezing/?fbclid=IwAR1Rv6gpWDE57LYYfeFSPQLa1tDIL7LfMQIoQhMrH0YDaiwSdGWDayoRMSA
- IBID
- Figure 4 and 5. Dr. Willie Soon. https://wattsupwiththat.com/2011/09/16/arctic-ice-refreezing-after-falling-short-of-2007/ and https://agupubs.onlinelibrary.wiley.com/doi/full/10.1029/2005GL023429
- IBID
- Figure 6 Lisiecki and Raymo (2005) http://what-when-how.com/global-warming/five-million-years-of-climate-change-from-sediment-cores-global-warming/
- Figure 7. Kobashi, T., K. Kawamura, J.P. Severinghaus, J.-M. Barnola, T. Nakaegawa, B.M. Vinther, S.J. Johnsen, and J.E. Box. 2011. High variability of Greenland surface temperature over the past 4000 years estimated from trapped air in an ice core. Geophys. Res. Lett., 38, L21501, doi:10.1029/2011GL049444. ftp://ftp.ncdc.noaa.gov/…/iso…/gisp2-temperature2011.txt
- Figure 8. https://pbs.twimg.com/media/DeuAH_4VMAAlBDd.jpg
- Figure 9. https://wattsupwiththat.com/2014/09/03/laughable-new-paper-claims-99-999-certainty-global-warming-over-past-25-years-is-man-made/
- Figure 10. https://wattsupwiththat.com/2011/02/28/visualizing-the-greenhouse-effect-atmospheric-windows/
- And https://thebestschools.org/special/karoly-happer-dialogue-global-warming/happer-major-statement/
- Figure 11. http://employee.heartland.edu/rmuench/carbondioxide.htm
- Figure 12. Sherwood Idso, PhD. http://www.co2science.org and https://thebestschools.org/special/karoly-happer-dialogue-global-warming/happer-major-statement/ Dr. Sherwood Idso with Eldarica pine trees grown in various amounts of CO2 in experiments done about 10 years ago when the ambient concentration of CO2 was 385 ppm. S.B. Idso and B.A. Kimball, “Effects of Atmospheric CO2 Enrichment on Regrowth of Sour Orange Trees (Citrus aurantium; Rutaceae) after Coppicing,” American Journal of Botany, 1994, 81: 843–846.
- Figure 13. https://www.geocraft.com/WVFossils/greenhouse_data.html Table 4a.
- 14. Sorokhtin et al. (2007) Sorokhtin, O.G., Chilingar, G. V., Khilyuk, L.F. (2007). Global Warming and GlobalCooling. Evolution of Climate on Earth,Developments in Earth & Environmental Sciences 5, Elsevier, ISBN 978-0-444-52815-5.
- 15. Climate Change Reconsidered. http://climatechangereconsidered.org/#tabs-1-2
- 16. https://budbromley.blog/2019/01/20/climate-impact-of-increasing-carbon-dioxide/
This article is re-published here:

Pingback: What if there is no Climate Emergency? – Watts Up With That?
Pingback: ≫ There is no Climate Emergency ! – Watts Up With That?
Your figure 1 says it all. The fundamentals of thermodynamics are easy to understand, and it is impossible for the atmosphere to warm the earth’s oceans and land masses. It would need to reach very high temperatures to do so. More importantly the 0.04% of CO2 has even less chance of changing the surface temperature.
I note a reference to the atmosphere acting as insulation. I can see the point, but most people think that insulation increases temperatures, which is implied here, but insulation slows down heat loss and I think that point should be stressed. Further, if we look at the surface temperatures on the moon, it is clear that the atmosphere also keeps the earth cooler in the daytime. The high humidity tropics are also cooler in the daytime compared with dry regions, although people will not think that because the humidity makes them feel warmer.
The article has one of the better descriptions of how IR is absorbed and emitted, but a key issue for me is that radiation is electromagnetic energy, not thermal energy and it only transfers as heat when the radiation complies with the laws of thermodynamics – heat only transfers in one direction, from hot to cold. Radiation, however, can travel in any direction.
I think the energy balance issue is important because obviously there isn’t an energy balance on short timescales and what I see is references to a temperature balance – incoming temperature from the sun is equal to the outgoing, which is utter nonsense. This is how the 33C warming of the greenhouse effect is derived.
What interests me, and I have not seen discussed, is that the earth’s average temperature as shown in ice core data does appear to be relatively stable. We only see a change in the temperature anomaly of about 12 degrees or so between ice ages and interglacial periods and this really is on a Kelvin scale, so a very small percentage change. How does such small variation cause the ice caps to expand and retreat?
You don’t mention the nitrogen and oxygen which we are told does not emit or absorb radiation and they only gain energy by collisions. It is impossible for collisions with greenhouse gases to heat and cool most of the atmosphere. Nitrogen and oxygen emit radiation, but it is not measured by IR thermometers and cameras. It is the characteristics of instrumentation that result in this nonsense.
An excellent article and more relevant than ever with the publication of the latest IPCC report.
LikeLiked by 1 person
Thanks for your comments and for reading. One point for understanding. Nitrogen and oxygen do not absorb in the main part of the longwave infrared (LWIR) spectrum under the conditions of earth’s troposphere. O2 and N2 are diatomic molecules and symmetric with no dipole moment in the troposphere. It is the multi-atomic molecules with dipole moments where we measure stretching and bending of atoms with regard to each other within the molecule that is being measured in infrared spectroscopy and which is equivalent to the measured LWIR absorption and emission such observed in CO2, H2O, CH4, etc. O2 does absorb and emit LWIR in the upper stratosphere after has absorbed ultraviolet. This is part of the process that creates ozone. Also, O2 absorbs in the near infrared. So, yes, the usual description of O2 and N2 is an artifact of the environmental conditions and IR instrumentation used. In the troposphere their energy transfer in the LWIR spectrum is kinetic from constant, frequent collisions rather than radiative. This is different in a vacuum or under extreme pressure. Remember, everything is measured relative to some standard, so what we think we know about everything (except the spirit world) is an agreed derivative of an arbitrarily defined condition, such as standard temperature and pressure (STP) is 25 degree C and 1 barr, around which is defined the periodic table. Temperature and pressure are derivatives. Since net global atmospheric CO2 concentration is controlled by Henry’s Law, Raoults Law and the Law of Conservation, and Henry’s Law is independent of the source of the CO2, then the radiative emission and absorption due to human produced CO2 are irrelevant to global temperature, climate change, greening, etc. CO2 concentration in air and ocean surface is the same today as it would be if humans never existed. The percentage of human produced CO2 in the atmosphere is irrelevant to climate.
LikeLike
Bud, you were doing fine until the last few sentences.
The amount of CO2 in the atmosphere (average “global atmospheric CO2 concentration”) is determined by its initial level plus the integrated sum of its sources and sinks. We have good measurement data which proves that every year, for at least the last 62 years, the sum of nature’s sources and sinks has been negative, and mankind’s has been positive. That is, mankind is adding CO2 to the atmosphere, and nature is removing it.
Thus nature has not caused the increase in the amount of CO2 in the atmosphere.
The one and only reason that the average atmospheric CO2 concentration has risen every year since precise measurements began in 1958 is that each year mankind has added more CO2 to the atmosphere than nature removed. Here are the data:
https://sealevel.info/global.1751_2014_2019.ems5_v07d.html
If humans never existed then the atmospheric CO2 concentration would be about 280 ppmv. The reason it is, instead, about 415 ppmv is that mankind has added about 215 ppmv, while nature removed only about 80 ppmv.
The temperature dependence of Henry’s Law is a minor factor. The rate of CO2 uptake by the oceans increases as atmospheric CO2 concentration increases, but it is slightly diminished by the temperature dependence of Henry’s Law. The capacity of the water to hold dissolved CO2 decreases by only about 3% per 1°C by which the water warms. That is very minor compared to the effect of a 48% rise in atmospheric CO2 level:
https://sealevel.info/feedbacks.html#co2watertemp
Here’s a graph:
LikeLike
Dave, your statement is wrong and easily dis-proven: “The temperature dependence of Henry’s Law is a minor factor.” See the graphic Principles of Aquatic Chemistry, by Francois Morel in this post: https://budbromley.blog/2021/08/18/henrys-law-controls-co2-concentration-not-humans/ Temperature of ocean surface is the dominant variable in the Henry’s Law phase-state equilibrium stoichiometry. Salinity, alkalinity, partial pressure changes (e.g. due to surface winds and ocean surface disturbances) cancel out at the global average level, but are important local variables. Try reading the references in that post. Also: https://budbromley.blog/2021/07/30/the-greenhouse-effect-can-be-as-good-as-rejected-and-henrys-law-stays-firmly-standing/
LikeLike
Dave, your statement is wrong and easily dis-proven: “The temperature dependence of Henry’s Law is a minor factor.” See the graphic Principles of Aquatic Chemistry, by Francois Morel in this post: https://budbromley.blog/2021/08/18/henrys-law-controls-co2-concentration-not-humans/ Temperature of ocean surface is the dominant variable in the Henry’s Law phase-state equilibrium stoichiometry. Salinity, alkalinity, partial pressure changes (e.g. due to surface winds and ocean surface disturbances) cancel out at the global average level, but are important local variables. Try reading the references in that post. Also: https://budbromley.blog/2021/07/30/the-greenhouse-effect-can-be-as-good-as-rejected-and-henrys-law-stays-firmly-standing/
LikeLike
If you have read my post https://budbromley.blog/2021/08/18/henrys-law-controls-co2-concentration-not-humans/ I hope you have already figured out why I was slow to respond to your comment. Basically, humans cannot control CO2 concentration in air and human CO2 emissions do not affect the net global atmospheric CO2 concentration or its trend. Therefore, the amount of absorption and emission of IR by/from human emitted CO2 is irrelevant to climate change and global warming. I certainly agree that IR radiation is electromagnetic energy, not thermal energy and have written that elsewhere on my blog. Thanks for reading and commenting.
LikeLike
Bud, you have produced an excellent overview of the fraudulent use of CO2 in the climate alarmism movement. I will link this article as a source reference for others so interested. I will also be using some of your discussion points in my future videos. To help expose the climate propaganda, I recently started making short, entertaining videos to try and reach the younger folks (such as this … https://www.youtube.com/watch?v=DNeujL1IoCA). Thanks again for your work on this subject.
LikeLiked by 1 person
Thanks for reading and thanks for the video. Good luck with your education project. Be sure you understand this one: https://budbromley.blog/2021/06/15/if-humans-never-existed-co2-concentration-would-be-the-same-as-it-is-today/ Let me know if I can answer any questions.
LikeLike
John, thanks for your work on the video. I have take the liberty to re-publish here on my blog. It took me a while to get to it because I do not have or want a YouTube account. Do you also publish your work on Rumble or BitChute for example? (I would rather not send people to YouTube either.) Thanks for reading and commenting and for your work. We should consider further collaboration.
LikeLike
Pingback: NZ National’s Election Strategy – Sto Vounó
Pingback: There is no Climate Emergency ! | US Issues
Pingback: Non c’è alcuna emergenza climatica! – Megachiroptera
Pingback: Non c'è alcuna emergenza climatica!